My personal information, just like yours, deserves the utmost safeguarding especially with the ever expanding digital landscape we find ourselves in today. My address, bank statements, credit card information, passwords and so forth should not be shared with anyone, let alone a complete stranger with bad intentions, but it somehow still gets accessed by those pesky thieves hiding behind screens.
Digitized solutions can inadvertently act as a minefield of compromising loopholes. Criminals are scouring systems for any vulnerability or flaw in the system that can be exploited.
You’re doing more than maintaining a fleet, you’re also running a business & trying to make a profit. The information and data you’re collecting holds monetary value that cyber criminals are looking to get in on. Protecting this valuable information is not just up to your IT guy, it’s also up to your entire team.
Incorporate privacy and security measures into the company’s daily operations
Go over privacy measures with your techs, drivers and team members. Review the company’s security policy and best practices to keep in mind while interacting with technology in daily operations.
Educate your team on the various ways cyber attacks can be presented to its unsuspecting targets and encourage everyone to limit password and information sharing. Inform them on popular forms of hacking such as phishing, virus infected links, copy-cat sites and tech-support scams, just to name a few.
They can be tricky to detect – let me give you an example: You open up your inbox to find a high priority email from someone claiming to be your telematics solution provider, asking you to log into your account via the intext link to verify your information and approve a system update. They warn that if you don’t, your subscription will be terminated by the end of the day. “Sure, why not?” you might think. You click the intext link, login, and click a couple of buttons – easy enough – you move on with your day. Unbeknownst to you, cyber-criminals then begin utilizing your credentials to access sensitive business information that could subject your company and it’s financial prosperity to a world of hurt.
Being aware is the first step to preventing an attack on your fleet. From there, develop a defense approach that can be taken should information be compromised. Additionally, make your team aware of the network tools and sites made available for their use and convenience. Curiosity killed the cat; don’t give them reason to aimlessly wander off into the world wide web, Lord knows what they’ll bring back.
Password protect sensitive information and be wary of using the same or similar variations of that login for different platforms. That’s like giving a cybercriminal a master key to all of the information you’re trying to protect.
Open communication and transparency will play an integral role in protecting company information. Make sure your team is aware of what is being collected, why and how it will be used going forward. Establishing a clear line of communication will allow everyone to be on the same page.
Aside from best practices for you and your team, it’s also a good decision to keep your software running on its A-game too.
Keep your systems updated and running on the latest software model
Each system update made available by software providers oftentimes comes with improved security features to better protect sensitive information and clears bugs from the system. Both of these factor into the overall security of your data.
Your IT team should notify end users every time a new hardware or software update is available. Setting up multi factor authentication for access to warranted systems additionally secure the assets ensuring the information doesn’t fall into the wrong hands.
Building transparency within internal operations can help you keep track of who is driving what vehicle, zero in on specific incidents and avoid over-reporting of events.
Invest in real-time threat alert system, privacy tools
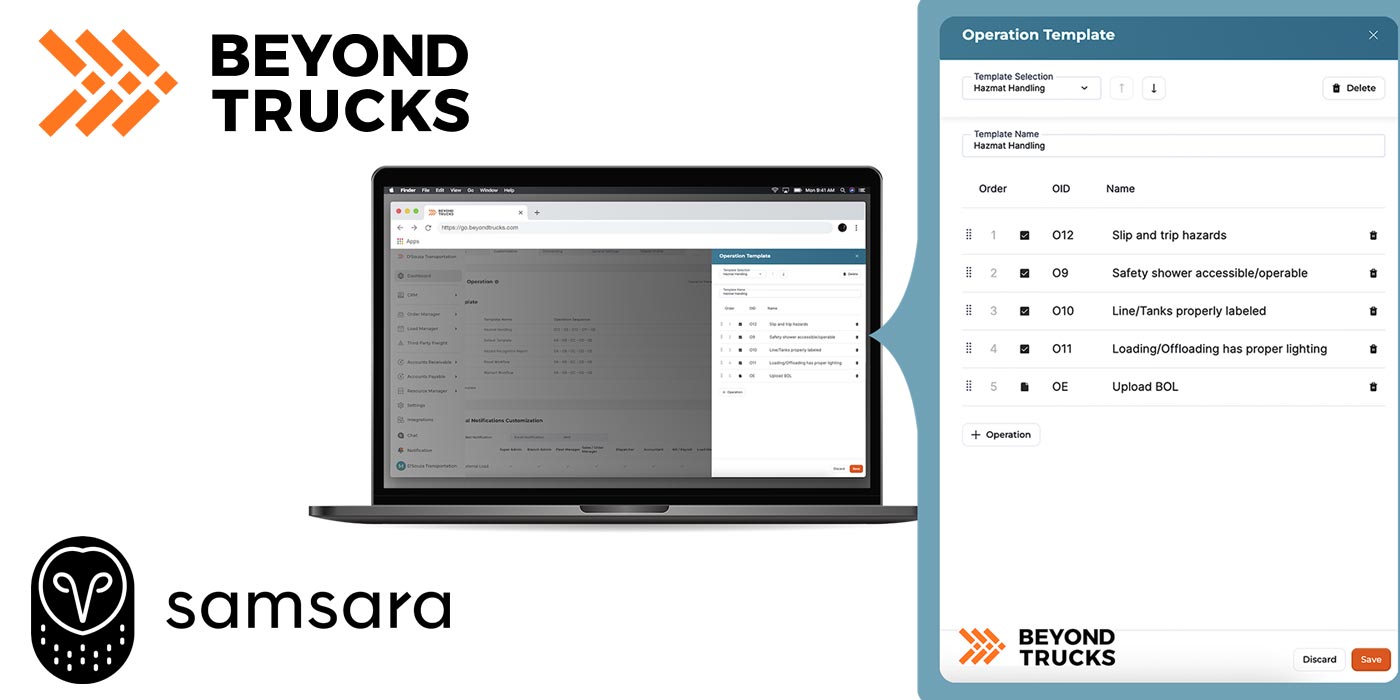
Take some time to explore potential software tools that you could use to protect company information. It’s also a good idea to do some research about what is offered by third party software providers to be sure they fit into your fleet’s cybersecurity plan. That can be found through the third party’s policies and procedures.
The utilization of real-time threat alert systems, such as motion-detection cameras, GPS tracking, and access control notifications, additionally ensures that any potential cause for concern can be promptly addressed and corrected to mitigate a situation’s severity.
This information, along with some help from your supplier of choice, can help you detect and prevent a security breach and its lasting negative effects on your fleet.
Fleet Equipment’s On The Road is sponsored by Rockland Flooring. Subscribe to our newsletter to catch every episode as we dive into the best practices and servicing information to keep your trucks On The Road.