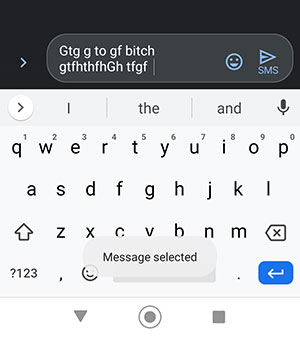
I was certain that my cell phone had been hacked. I had been scrolling through search results in the browser app when I got a text message from my father-in-law. The phone, by itself, switched to the text messaging app, typed a gibberish message (except for the swear word that was spelled correctly) and sent a response I didn’t type. That’s when the paranoia hit. Hard.
If someone could take control of my phone, then they could also see my screen. If they could do that, then they could record every keystroke–they would have every password to any account I ever used on my phone. Basically my entire personal and financial life splayed open for hackers to see since … when? Yesterday? A month ago? The beginning of time? I had to assume the worst.
So I factory reset my phone and used a different device on a different network to reset all my passwords. Sure, I could have assumed it was a “ghost touch” issue—a defect in the touchscreen—to which my Android phone is prone, but the fact is that the possibility that my phone was hacked was enough to scare me into immediate action. This is the world we live in now, where so much of our lives are managed over a cellular signal. And this was just my phone that I use to answer emails and share stupid memes.
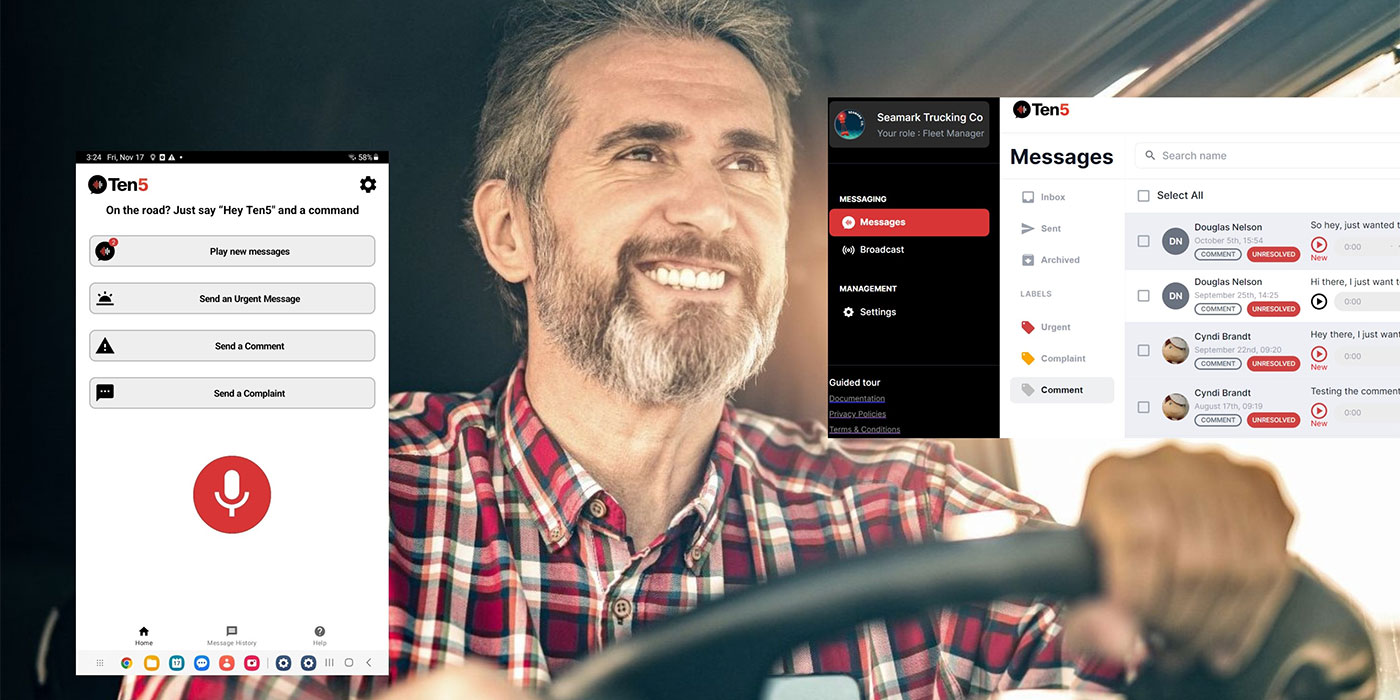
What if this was a truck? Your truck.
What information would a hacker be able to see? Equipment operation specs, service data, your routes, your delivery location? What other sensitive business data is that tied to?
Headlines of cyberattacks are growing. In 2020, the number of cyberattacks set records. They also got smarter. The SolarWinds attack, in which a Russian intelligence service snuck malicious code into the Texas-based company’s software update, demonstrated how sophisticated and real the threats can be. This year’s Colonial Pipeline ransomware attack took aim at an infrastructure cornerstone, one that moves about 45% of all fuel consumed on the East Coast.
It’s time for fleets to take cybersecurity seriously, and this isn’t just a responsibility for your IT department—everyone plays a role in cybersecurity.
“SolarWinds is escalating the security problem to a new level,” said Neil Cawse, Geotab’s chief executive officer. “What I think is more important is that the SolarWinds exploit highlights the huge vulnerability we all face in the entire software supply chain. All software is built and managed using other software. If that software is compromised anywhere, then we are all vulnerable.”

Cawse noted that this is a wake-up call for all software companies. While the onus of cybersecurity starts with the developer you’re working with to power your truck technology solutions, you too should be vigilant.
“Customers don’t have to worry too much that the ransomware operations will be using [the SolarWinds tactic] in a big way, but where there are vulnerabilities, there are risks,” Cawse said. “Tightening up the number of third parties you use in your own organization, making sure your company has a strong security program and training IT and staff on exploit possibilities has now become even more key.”
Now, the problem is we can’t print exactly what you need to do to ensure your business is secure—that would create a starting point for would-be hackers—but we can point you in the right direction. Your cybersecurity responsibility resides in the conversations you have with your external industry partners, from OEMs and suppliers to telematics and ELD providers, as well as your internal colleagues, from IT personnel to drivers.
So here are a few resources to help get the conversations started and help you feel at ease talking about a complicated topic.